Terminal Server
There are two configuration options:
- securityProtocolTypesForOutboundCommunication defines the TLS protocol for the Terminal Server when it acts as a client, typically in situations:
- OpenAPI 5.6 plugin: Calls to MFDs initiated by the Terminal Server.
- All other HTTP calls initiated by the Terminal Server, such as calls to MFDs, Dispatcher Paragon Payment System, and Dispatcher Paragon Infrastructure Service.
- securityProtocolTypesForServerRole defines the TLS protocols for the Terminal Server when it acts as a server. Currently, this option controls:
- LDAP in Terminal Server
- OpenAPI 5.7 plugin: From 6.0.99 we are using OpenAPI 5.7 as default and this handles TLS 1.3 well
OpenAPI 5.6 plugin: Calls initiated by MFDs, such as card authentication.
We suspect that the KM SDK is not handling TLS 1.3 correctly, resulting in timeouts.
Issue is being investigated by KM under CS0523709.
From our experience, the best workaround is to disable TLSv1.3 on the MFD.In version 6.0.97, TLS 1.3 for OpenAPI 5.6 is temporarily disabled. Therefore, when using version 6.0.97 or later, there is no need to disable TLS 1.3 on the MFDs.
In addition to the configuration options listed above, it may be necessary to alter Windows Server configuration. For instance when the Terminal Server acts as a server for SQTA/SQTS, the configuration cannot be directly modified in Dispatcher Paragon, and the Terminal Server uses the lowest supported security protocol allowed by the operating system. To adjust the Windows Server configuration either modify the registry (official documentation) or use an external tool like IIS Crypto.
Checking available protocols
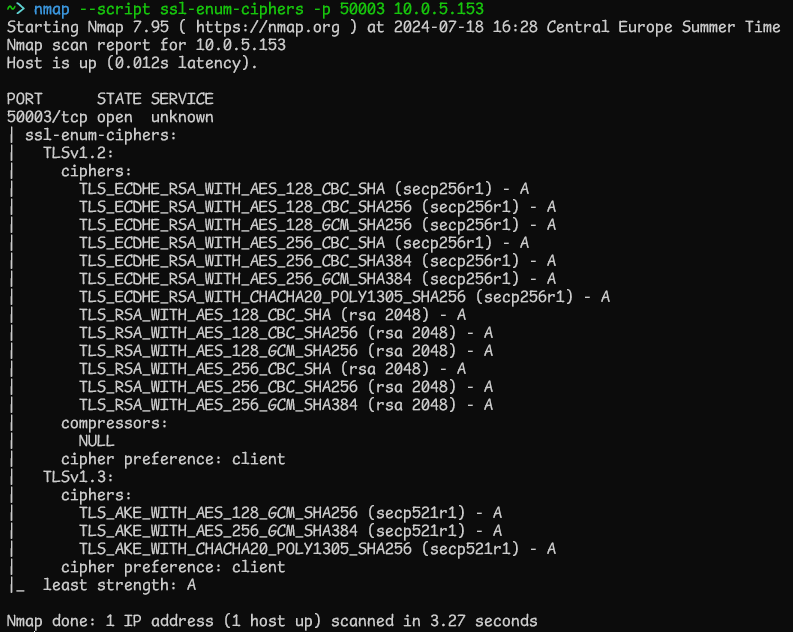
To check if the MFD supports TLS 1.3, you can use tools like Nmap. Nmap can also determine which protocols are available on server ports. Although the port number varies by vendor, port 443 is commonly used. For example, to verify a Konica Minolta device, you would perform the following steps:
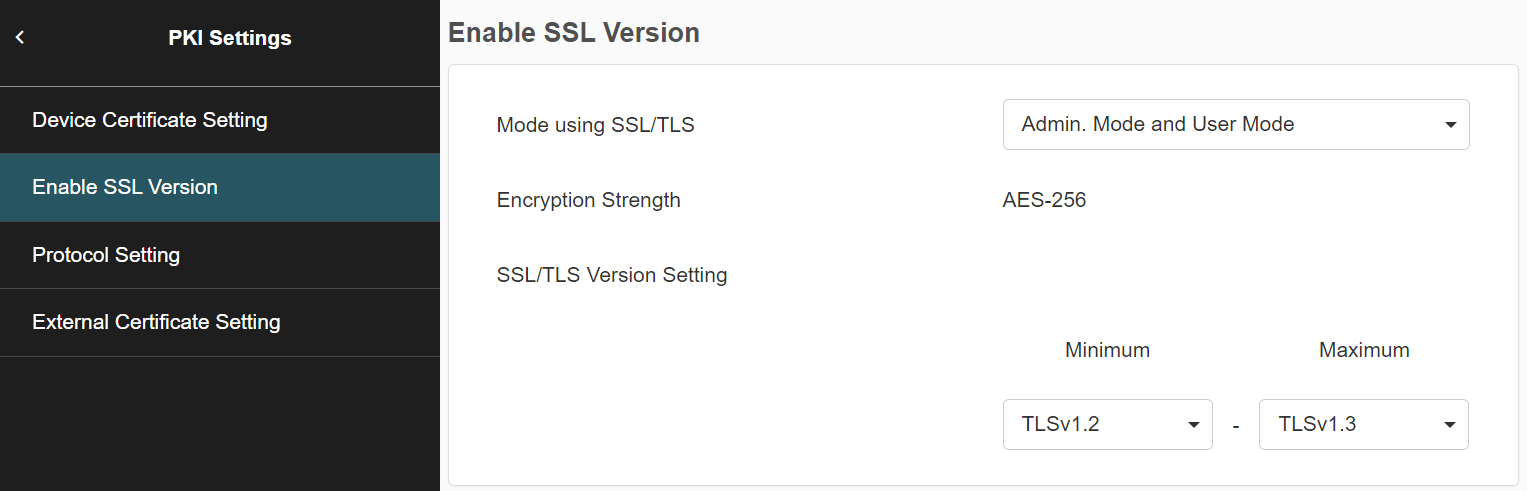
Konica Minolta Device Configuration
For Konica Minolta devices, the TLS protocols can be set on the MFD configuration page:
TLS 1.3 is not supported when using OpenAPI SDK versions 4.2 and 4.13a. The used version is specified by the kmOpenApiVersion configuration option.
Management
There is a complete guide Configuring SSL/TLS for Dispatcher Paragon Management Service.
Dispatcher Paragon Job Service
There are two configuration options:
- jobServiceSecurityProtocolTypesForClientRole defines the TLS protocol for the Job Service when it acts as a client, typically in situations:
- Communication with other Job Services in a cluster
- Calls to identity providers such as Entra ID
- jobServiceSecurityProtocolTypesForServerRole defines the TLS protocol for the Job Service when it acts as a server, typically in situations:
- Communication from the Dispatcher Paragon Client v3
- Requests by any consumer of the Job Service API
Dispatcher Paragon Client v3
There are two configuration options:
- spoolerSecurityProtocolTypesForClientRole defines the TLS protocol for the Client v3 when it acts as a client, typically in situations:
- Communication with Job Services
- Communication with Client v3 in server mode
- Communication with MFDs via the IPPS backend
- spoolerSecurityProtocolTypesForServerRole defines the TLS protocol for the Client v3 when it acts as a server, typically in situations:
- Communication from the Dispatcher Paragon Client v3 in client mode
- Communication from any IPP client using Client v3 in server mode as an IPP server
- Communication with MFDs via the IPPS backend